The Spyderbat Platform
Spyderbat instantly and continuously visualizes all runtime app behavior—
from the kernel to the cloud—to reduce alerts by 2-3 orders of magnitude, and automatically block attacks in real time.
Trusted in Production





Continuous Runtime Protection
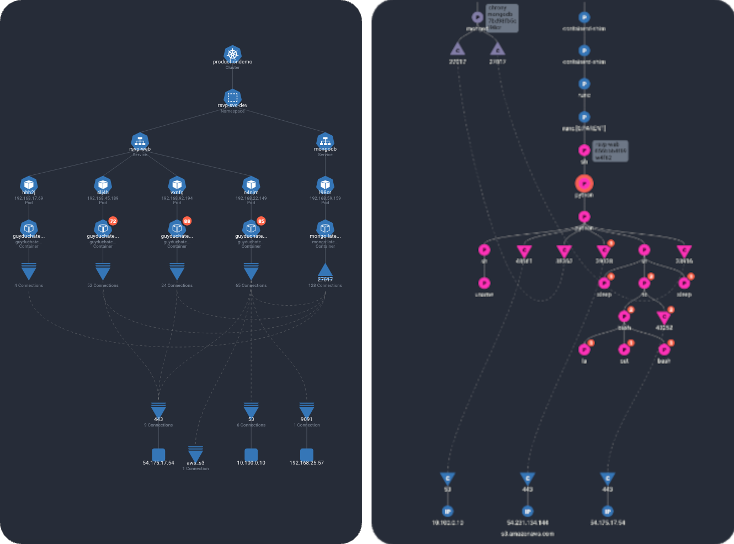
- True continuous monitoring: Capture runtime context to surface risk in real time, without overwhelming alerts.
- Critical causal context: See clear chained events that pinpoint exactly what went wrong, when it happened, what led to it, and the potential for downstream impact.
- Visibility and control for Day 2: Automatic guardrails protect known-good processes, and stop anomalies that lead to outage, downtime and risk.
Negligible impact to system performance, no code changes for developers, fully automated profiling—and no more log digging
Recent Recognition and Shouts
A sampling of freshly minted industry awards, customer testimonials,
and general Spyderbat celebration
Security Time Travel
"...Their platform has distinct components that allow you to see things as they were, as they are, and how they should be."
Read the Article

From the Experts
"Spyderbat is an amazing option for companies looking for rich Kubernetes specific runtime protection"
- James Berthoty, DevSecOps

Startup of the Year
Spyderbat Named “Cloud Security Startup Of The Year” based on innovation and success in information security.
Read the announcement

Cloud Speed, Cloud Scale
Built for the culture of continuous improvement
Automate away the manual investigation and interrupts that come from root cause analysis. Build more. Dig less.
 Limit Interruptions
Limit Interruptions
Buy time to patch on your own schedule with active protection against attacks targeting known vulnerabilities.
 Instant Protection
Instant Protection
Guardian policies detect application drift from built-in Linux services, Kubernetes services, and common commercial applications providing the most resilient defense against drift, as well as unknown and zero-day attacks.
 Clear Value
Clear Value
Detections are mapped to the MITRE ATT&CK Matrix, and Flashback visually shows chained TTPs for both existing and never-before-seen threats.





