Threat Detection, Investigation, and Response for Cloud, Kubernetes, and Linux
Find and stop threats in real time, without false positives and overwhelming alerts for hybrid cloud, multi-cloud, Kubernetes and Linux
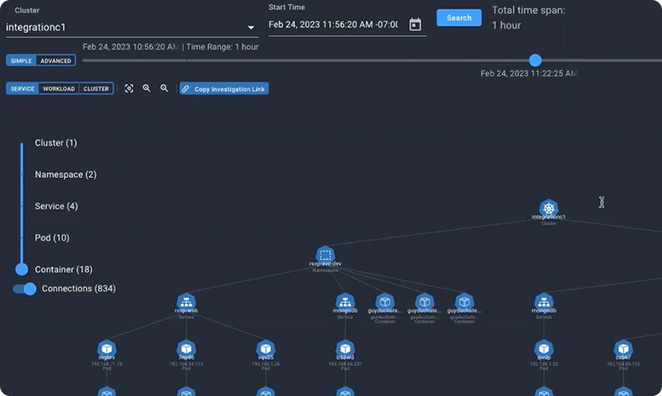
The Spyderbat Platform
By connecting eBPF data plane runtime activities with control plane context, Spyderbat links workload and user behavior by their causal relationships to form the Behavioral Context Webtm. With this foundation, Spyderbat detects at runtime when your applications drift, recognizes the chained evidence of an attack, and automates responses with immediate visibility to an issue's root cause using less than 2% of cloud resources.
Learn More about Spyderbat's cloud detection and response and the differences between CDR & posture management here >>
Flashback
Instant root cause
Like a DVR, playback your runtime applications and user activity across both data and control planes in interactive visualizations to resolve issues in seconds, not days.
- Eliminate the pain of scanning logs to determine the source of service interruptions and attacks.
- Stop finger pointing by automatically pinpointing root cause.
Guardian
Detect application drift
Spyderbat’s Guardian continuously compares running applications against prior versions to recognize drift, providing the insights needed to take instant action to get your application back on track.
- Stop misconfigurations, supply chain compromise, and new, evasive attacks.
- Maximize uptime and development speed while staying secure.
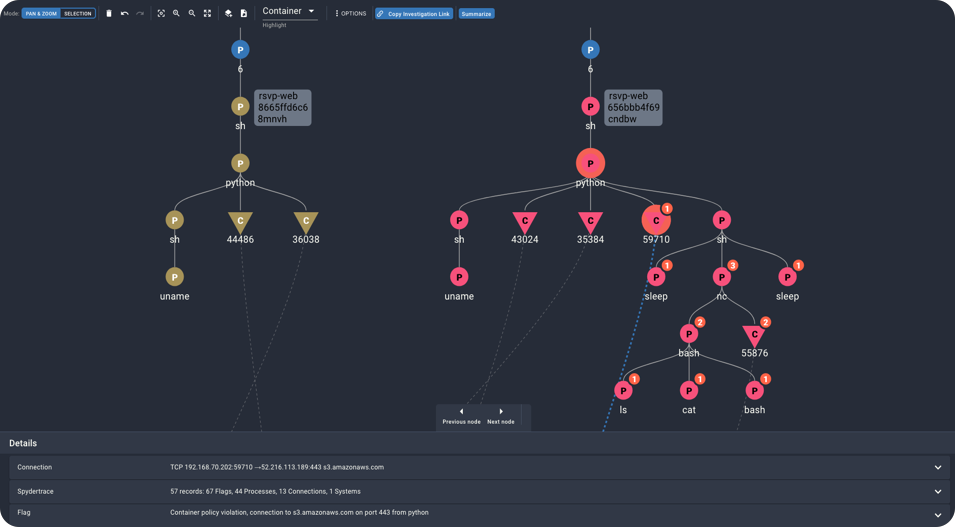
Scout
Detect attacks without alert overload
Scout accurately recognizes attacks by automatically chaining tactics and suspicious behaviors together, spanning across data and control planes. Using the Behavioral Context Web, Scout exponentially reduces false positives without missing attack indicators.
- Stop attacks targeting known and even unknown vulnerabilities, including:
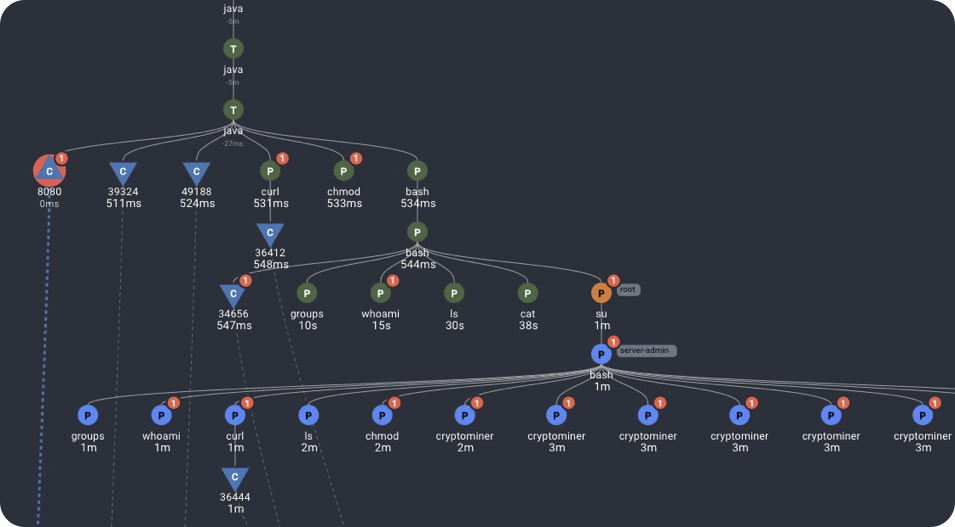
- Malware, including Ransomware.
- Crpytojacking.
- Zero-Days.
- Stolen credentials and insider threats.
- Recognize threats early with detections mapped to MITRE ATT&CK cloud, container, and Linux tactics to gain a full understanding of scope and entry.
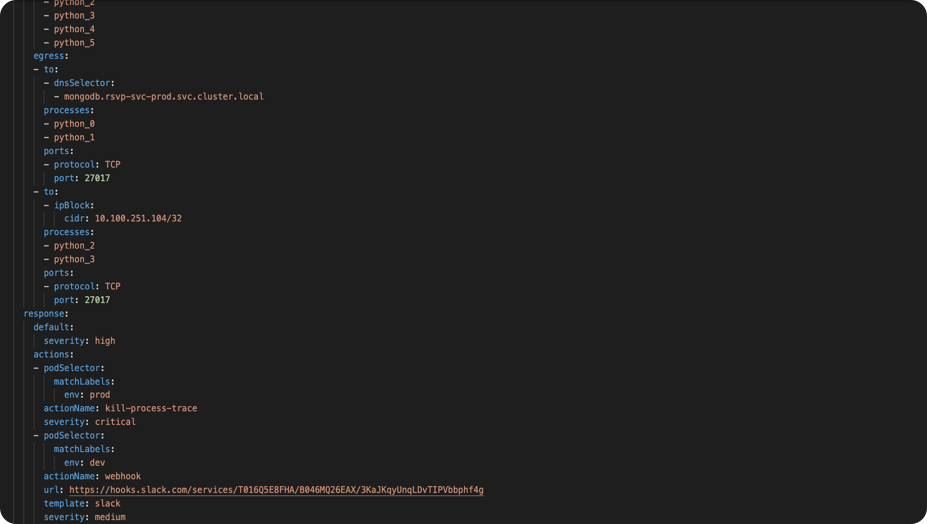
Interceptor
Minimize response time and maximize uptime
Programmatically stop threats, block errors, and notify the right teams at the right time. With Interceptor, take automated actions from insights raised by Guardian and Scout.
- Minimize interruptions and work the way your team wants to work.
- Low friction integration with existing cloud tooling and GitOps culture.
Spyderbat Labs
Cloud-native threat research
Spyderbat Labs performs threat research to produce ongoing actionable intelligence updates to the Spyderbat platform.
- Instead of relying on individual Indicators of Compromise (IOCs), Spyderbat Labs develops detections mapped to the MITRE ATT&CK Matrix and Microsoft's Kubernetes Threat Matrix.
- Labs findings power the Spyderbat Behavioral Context Web to connect causally-related detections, and recognize emerging attacks and application drift accurately.
Seeing is Believing
See how Spyderbat transforms threat response for cloud native app runtime









