Spyderbat Scout
Our cloud native environments change at a rapid pace, creating the optimal scenario for threat actors to gain footholds and take action on their objectives. The same rate of change creates new challenges in identifying true attack activity.
Spyderbat Scout observes workload behaviors in real-time, automatically chaining together attack indicators for early and accurate recognition.
Instead of chasing down individual detections plagued with overwhelming noise, false positives, and blind spots, instantly identify real attacks based on chained suspicious behaviors.
1000:1*
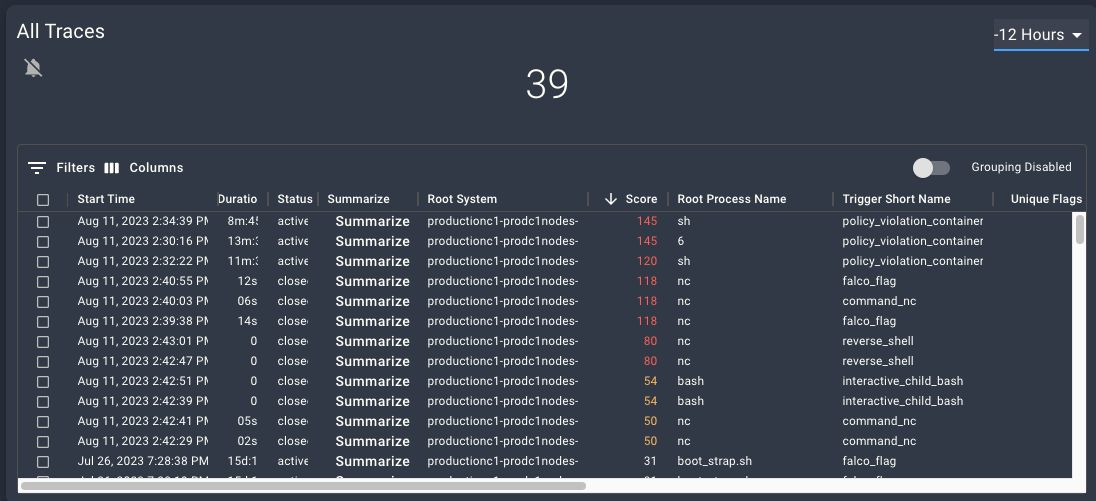
Wouldn't you like to reduce your false positives by 1000 to 1? Look, we are just as skeptical of grandiose Marketing numbers so we are happy to let the product speak for itself. Discover how Spyderbat’s chained attack indicators suppress would-be false positives with unique Spydertraces, risk scoring every sequence of activity in your containerized environments.
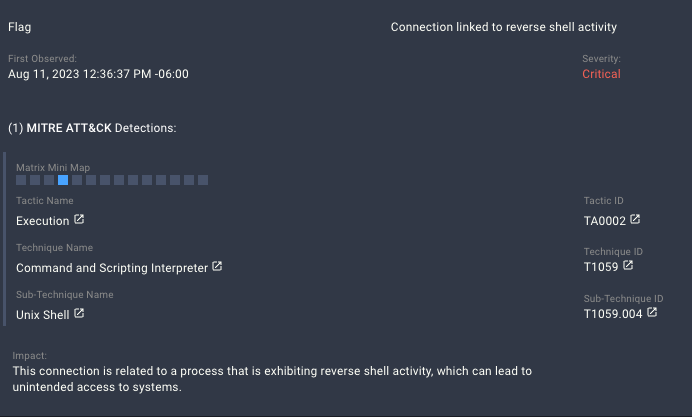
Spyderbat Flags
Continually colors the Spyderbat Behavior Context Web with risk.
- Spyderbat identifies suspicious activities as they occur, adding 'flags' to Spyderbat's Behavioral Context Web.
- Spyderbat’s detections cover the attack tactics in MITRE's ATT&CK Matrix for Linux and Kubernetes.
- Add your own detections from third-party systems to see their findings in context with preceding and subsequent activities to get the full picture.
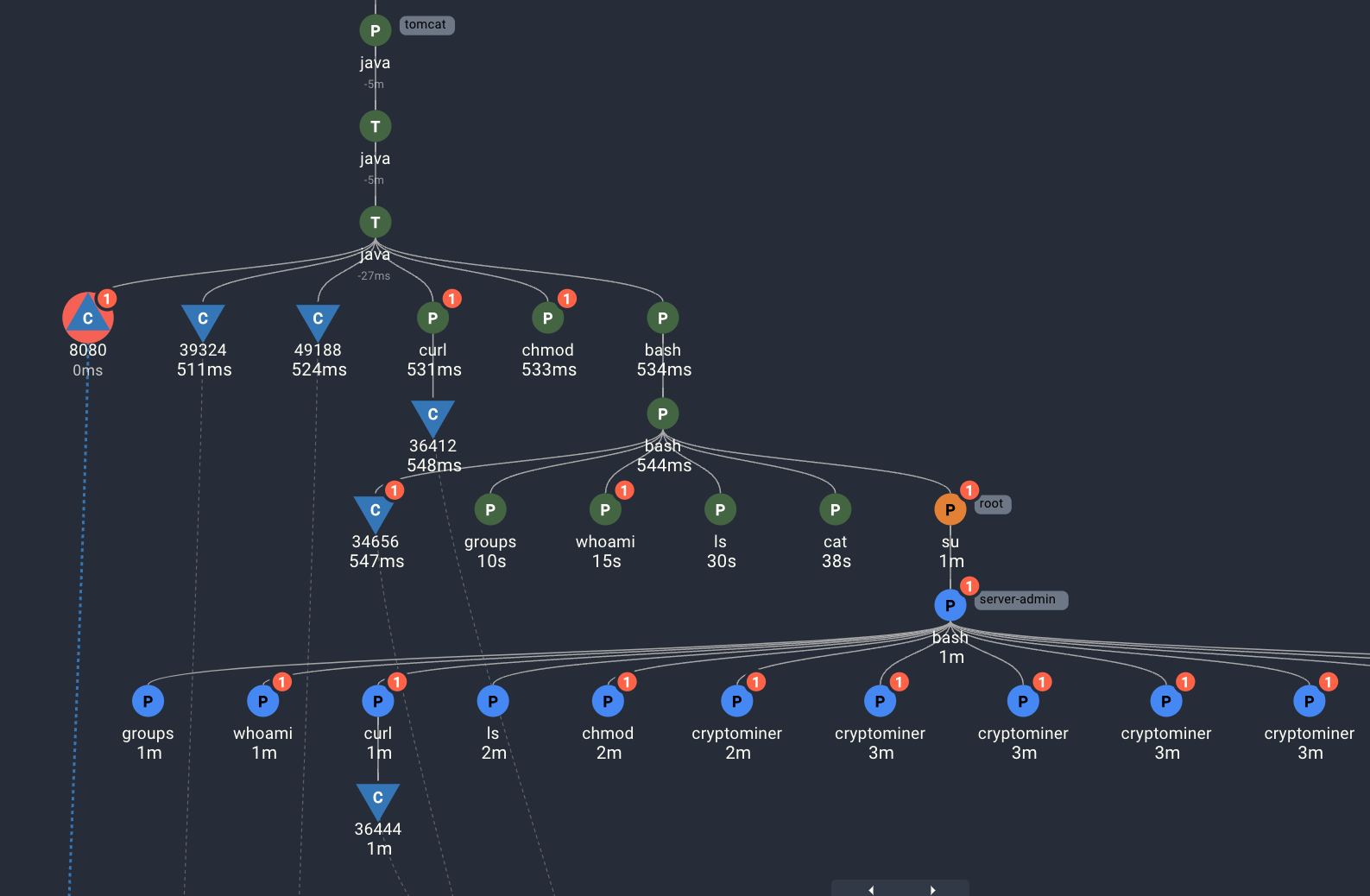
Spydertraces
Automatically chains together attack indicators based on their causal relationships.
- The Behavioral Context Web automatically connects suspicious activities together, even if separated across systems, user sessions, and long periods of time.
- Each red circle in the screenshot indicates one or more Spyderbat Flags set on the corresponding process or network connection.
- Immediately see the current progression of the attack with its origination point, even if weeks prior.
- See the full forensic details exactly as it occurred even across ephemeral containers no longer available or in a changed state.
Spyderscores
Reassesses the risk of a Spydertrace with any new activity.
- Spyderscores account for the number of flags, the variety of flags, flag severity, as well as depth of activity and environmental factors.
- Spyderbat scales to monitor thousands to tens of thousands of Spydertraces simultaneously, acting as a watchdog to take action the moment a Spyderscore shoots up.
- Only this approach reliably catches
- Low-and-slow attacks.
- Malware (e.g. Ransomware, Cryptojacking) with long, random wait times.
- Subversive backdoors.
- True zerodays.