Runtime Security for AWS
Secure your AWS runtime environment with Spyderbat across EC2, managed container services such as Amazon ECS for container orchestration, and Amazon EKS for Kubernetes-based deployments.

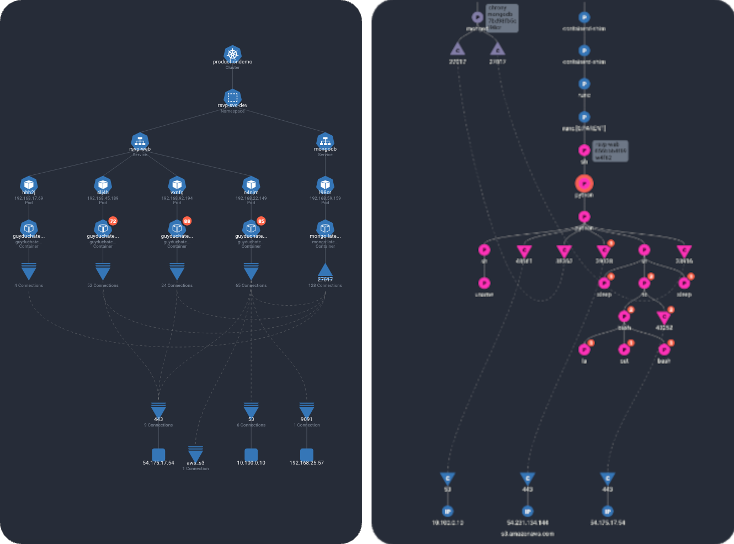
Spyderbat complements AWS native tools, such as Cloudtrail and GuardDuty, with a living map of activities connecting system, container, and network activity continuously assembled by their causal linkage sequences. From pre-to-post production, Spyderbat proactively monitors every EC2 instance, tracking thousands of system-level traces, to raise accurate, actionable insights.
Signatureless detection of compromised EC2 instances EKS workloads
Spyderbat automatically chains together an attacker's tactics and techniques for early and accurate attack detection.
- Spyderbat’s trace-based analytics identifies true attack behavior with low signal-to-noise.
- Go beyond logs - get the complete picture, including AWS Tags and EC2 properties, to immediately see the full scope and entry point of real attacks.
- Catch ‘low-and-slow’ attacks that span user sessions, systems, and even long periods of time (months).

Detect and instantly root cause misconfigurations and errors
Spyderbat instantly recognizes drift of Linux services on EC2 nodes and EKS container workloads.
- Catch runtime 'surprises' early in the development process that would otherwise disrupt your production uptime.
- Immediately get the who, what, where, and how of issues.
- Protect yourself from supply chain compromises by detecting unexpected changes in third-party components.

READY TO SEE SPYDERBAT IN ACTION?
Automate your AWS SecOps with Spyderbat.
Let our experts show you how Spyderbat turns eBPF and container runtime data into real-time insights and actions, so you can fully visualize and protect your EC2 and EKS environments.



